## Jeesns Weibo store XSS
### Introduction to Vulnerability
JEESNS is a social management system based on JAVA enterprise-level platform. Based on the advantages of enterprise-level JAVA, such as high efficiency, security and stability, it creates a pioneering domestic Java version of open source SNS. JEESNS can be used to build portals, forums, communities, Weibo, Q&A, knowledge payment platform, etc. In Jeesns <= 1.4.2, the input to the weibo user's input filtering is incomplete, resulting in a stored XSS vulnerability.
### Vulnerability Impact
* Jeesns <= 1.4.2
### Vulnerability Analysis
The data submitted by the user foreground will pass XSSFilter, and the doFilter will call XssWrapper.
```java
Package com.lxinet.jeesns.core.utils;
Import java.util.regex.Matcher;
Import java.util.regex.Pattern;
Import javax.servlet.http.HttpServletRequest;
Import javax.servlet.http.HttpServletRequestWrapper;
Import org.springframework.web.util.HtmlUtils;
Public class XssWrapper extends HttpServletRequestWrapper {
Private static final String REGEX_SCRIPT = "<script[\\s\\S]*?<\\/script>";
Private static final String REGEX_STYLE = "<style[^>]*?>[\\s\\S]*?<\\/style>";
......
Public String getParameter(String parameter) {
String value = super.getParameter(parameter);
Return value == null ? null : this.cleanXSS(value);
}
Public String getHeader(String name) {
String value = super.getHeader(name);
Return value == null ? null : this.cleanXSS(value);
}
Private String cleanXSS(String value) {
Value = dealScript(value);
Value = dealStyle(value);
String[] eventKeywords = new String[]{"onmouseover", "onmouseout", "onmousedown", "onmouseup", "onmousemove", "onclick", "ondblclick", "onkeypress", "onkeydown", "onkeyup", "ondragstart", "onerrorupdate", "onhelp", "onreadystatechange", "onrowenter", "onrowexit", "onselectstart", "onload", "onunload", "onbeforeunload", "onblur", "onerror", "onfocus ", "onresize", "onscroll", "oncontextmenu", "alert"};
For(int i = 0; i < eventKeywords.length; ++i) {
Value = value.replaceAll("(?i)" + eventKeywords[i], "_" + eventKeywords[i]);
}
Return value;
}
Private static String dealScript(String val) {
Pattern p = Pattern.compile("<script[\\s\\S]*?<\\/script>");
Return htmlEscape(p, val);
}
Private static String dealStyle(String val) {
Pattern p = Pattern.compile("<style[^>]*?>[\\s\\S]*?<\\/style>");
Return htmlEscape(p, val);
}
Private static String htmlEscape(Pattern p, String val) {
String s;
String newVal;
For(Matcher m = p.matcher(val); m.find(); val = val.replace(s, newVal)) {
s = m.group();
newVal = HtmlUtils.htmlEscape(s);
}
Return val;
}
}
```
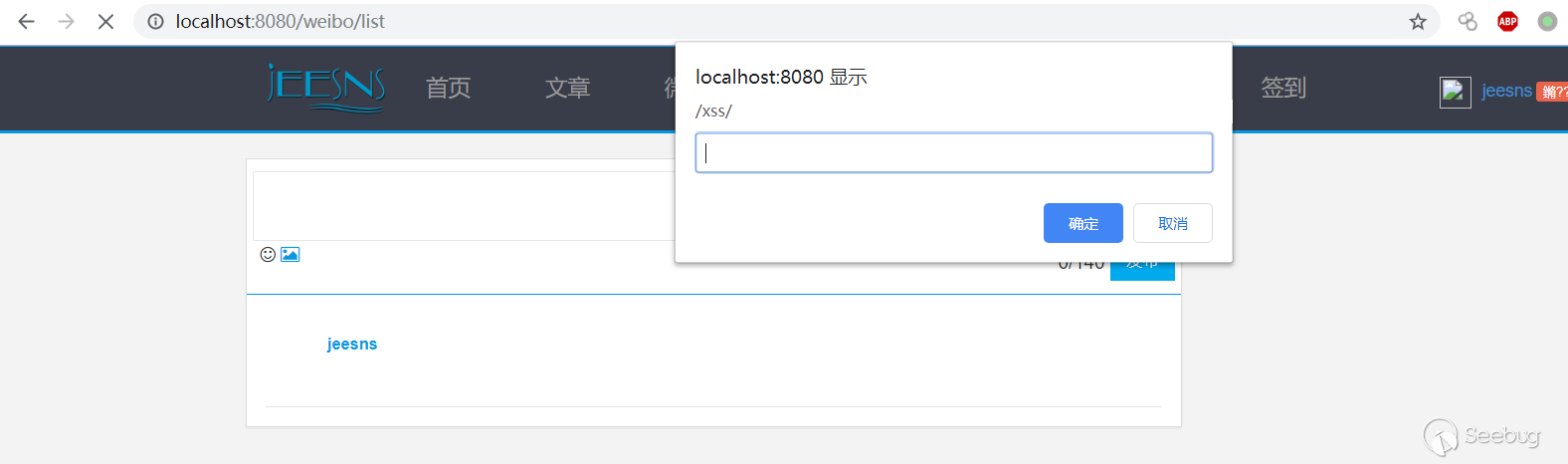
As you can see, the `<script>` and `<style>` tags are filtered, and some HTML events are escaped and filtered. However, when matching tags, there is no case processing, which can be bypassed by capitalization.
See the `save()` of the function `\jeesns-service\src\main\java\com\lxinet\jeesns\service\weibo\impl\WeiboServiceImpl.java` where the weibo is saved.
```java
@Override
@Transactional
Public boolean save(HttpServletRequest request, Member loginMember, String content, String pictures) {
If("0".equals(request.getServletContext().getAttribute(ConfigUtil.WEIBO_POST.toUpperCase())))){
Throw new OpeErrorException("Weibo is closed");
}
ValidUtill.checkIsBlank(content, "Content cannot be empty");
If(content.length() > Integer.parseInt((String) request.getServletContext().getAttribute(ConfigUtil.WEIBO_POST_MAXCONTENT.toUpperCase()))))
Throw new ParamException("Content cannot exceed "+request.getServletContext().getAttribute(ConfigUtil.WEIBO_POST_MAXCONTENT.toUpperCase())+"word");
}
//Get the topic
String topicName = TopicUtil.getTopicName(content);
WeiboTopic weiboTopic = null;
If (StringUtils.isNotBlank(topicName)){
weiboTopic = weiboTopicService.findByName(topicName);
If (weiboTopic == null){
weiboTopic = new WeiboTopic();
weiboTopic.setName(topicName);
weiboTopicService.save(weiboTopic);
}
}
Weibo weibo = new Weibo();
weibo.setMemberId(loginMember.getId());
weibo.setContent(content);
weibo.setStatus(1);
If(StringUtils.isEmpty(pictures)){
//Ordinary text
weibo.setType(0);
}else {
//image
weibo.setType(1);
}
If (weiboTopic != null){
weibo.setTopicId(weiboTopic.getId());
}
Int result = weiboDao.saveObj(weibo);
If(result == 1){
@@会员处理 and send system messages
messageService.atDeal(loginMember.getId(),content, AppTag.WEIBO, MessageType.WEIBO_REFER,weibo.getId());
pictureService.update(weibo.getId(),pictures, content);
actionLogService.save(loginMember.getCurrLoginIp(), loginMember.getId(), ActionUtil.POST_WEIBO,"", ActionLogType.WEIBO.getValue(), weibo.getId());
/ / Post microblogging rewards
scoreDetailService.scoreBonus(loginMember.getId(), ScoreRuleConsts.RELEASE_WEIBO, weibo.getId());
}
Return result == 1;
}
```
The data of the user condition is not further filtered, and is directly saved to the database, and then the front end directly renders, resulting in a storage type XSS.
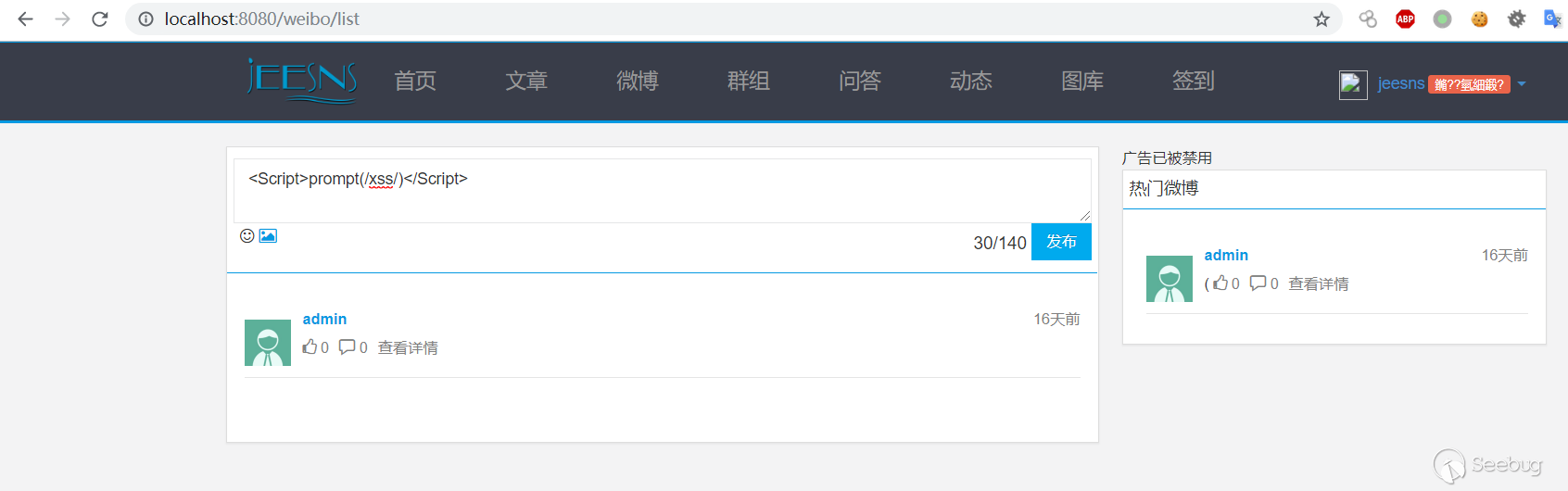
### Vulnerability recurrence
1. Register a user
2. Post the Weibo and fill in the XSS payload `<Script>prompt(/xss/)</Script>`.
3. Trigger XSS when viewing the Weibo.


暂无评论