Our vulnerability-scanning system at PeckShield has so far discovered several dangerous smart contract vulnerabilities ( batchOverflow[1], proxyOverflow[2], transferFlaw[3], ownerAnyone[4], multiOverflow[5], burnOverflow[6]). These vulnerabilities typically affect various tokens that may be publicly traded in exchanges. Today, we would like to report a new vulnerability named ceoAnyone, which affects, instead of tradable tokens in exchanges, but Crypto-Games.
Starting from the end of 2017, blockchain-based crypto-games have become popular especially with the initial success of [CryptoKitties](https://www.cryptokitties.co/). Among crypto-games, cypto idle game is an interesting category that enables players to make money by idling for hours, then followed by a profit-making transaction (e.g., selling a Lab Rat on [Ether Goo](https://ethergoo.io/)). Many of the cypto idle game owners make profit from the transaction fee. However, what if the owner address could be manipulated or completely hijacked by attackers?
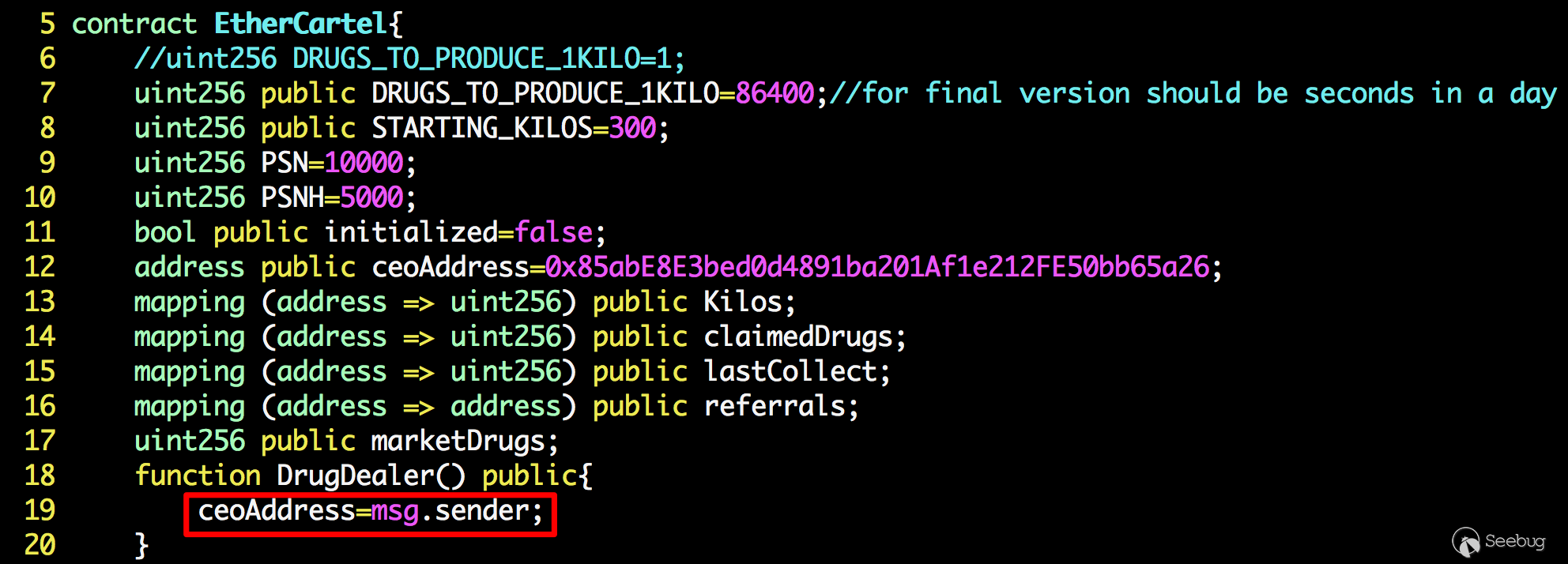
Figure 1: A ceoAnyone-affected Crypto Idle Game Smart Contract
Figure 1 illustrates such a smart contract of a crypto idle game named Ether Cartel. Similar to [Ether Shrimp](https://dapptotal.com/) Farm that requires end users to hatch and sell shrimp in a bid to maximize production before ultimately exchanging eggs for ether, Ether Cartel takes the same concept but applies it to drug running. The game “features a high tech automated market that lets you instantly buy or sell drugs with a single transaction. The more kilos you have, the more drugs they produce (each kilo produces at a rate of 1 per day). Collect more kilos with your drugs to multiply your production.”

Figure 2: A Crypto Idle Game -- Ether Cartel
Ether Cartel was deployed in mainnet on Friday, May-18-2018 05:14:56 PM +UTC. Unfortunatley, it was exploited on the same Friday, May-18-2018 06:25:12 PM +UTC, within 1 hour and 11 minutes after deployment! The vulnerable code is in lines 18-20: there’s a public function named DrugDealer() which allows the caller to change the beneficiary address — ceoAddress.
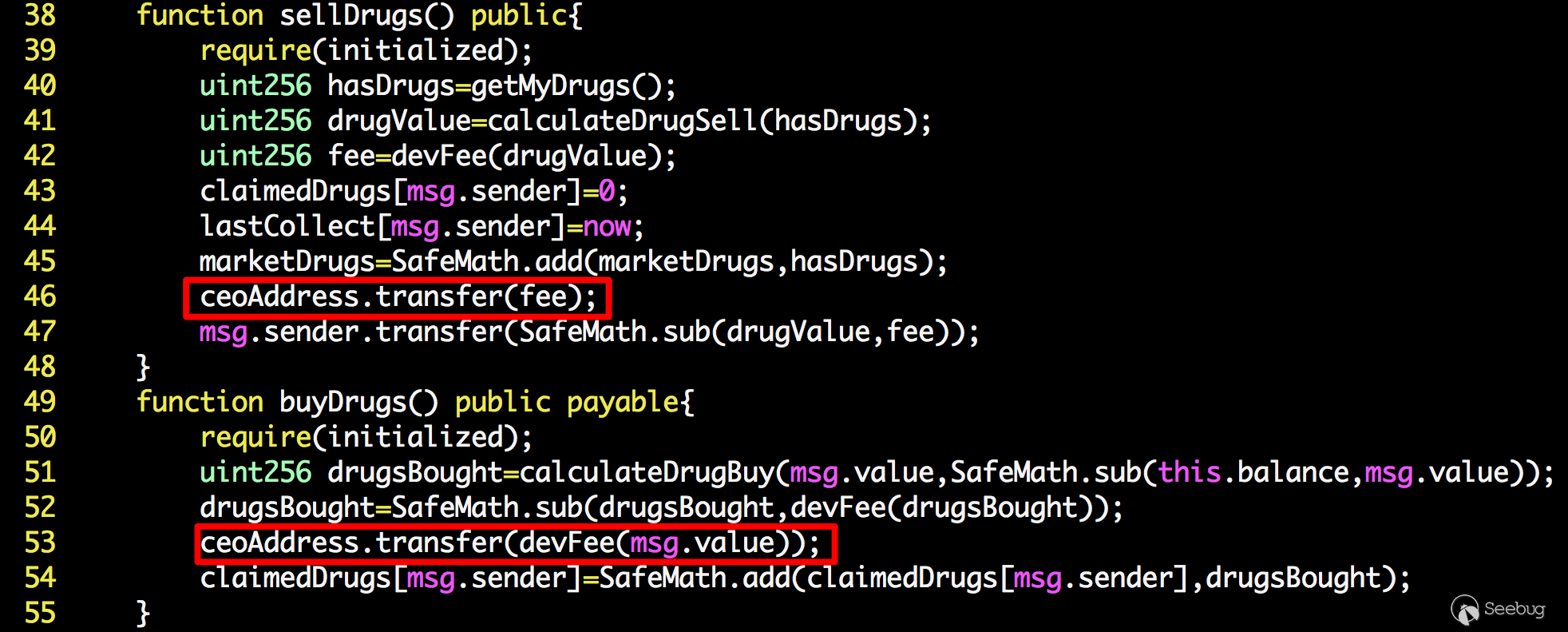
Figure 3: A ceoAnyone-affected Crypto Idle Game Smart Contract
As shown in Figure 3, the ceoAddress collects the fee whenever sellDrugs() or buyDrugs() is called. Our analysis shows that this particular game has three versions of smart contracts deployed by the same author. After cross-examining these contracts, we have the reason to believe that the buggy drugDealer() is actually the constructor of the smart contract. However, the author accidentally gave it a wrong name (not identical to the contract name). This seems to be a classic problem that has been studied since 2016 (the Rubixi contract was pointed out to have a similar bug in [7]).
As of writing this blog, we have found multiple attackers are gaming to exploiting this vulnerability. And one particular attacker seems to monitor the change of ceoAddress and will immediately regain the control if it has been modified by others. (One attacker has collected around 1.6 ETH by exploiting this vulnerable Ether Cartel game.) After identifying this particular vulnerability, we immediately made the efforts to contract the author. Also, our internal scanning shows that some other smart contracts of similar crypto games have the same problem. We are now contacting these affected development teams by providing necessary technical support.
About US
PeckShield Inc. is a leading blockchain security company with the goal of elevating the security, privacy, and usability of current blockchain ecosystem. For any business or media inquires (including the need for smart contract auditing), please contact us at telegram, twitter, or email.


暂无评论